Internet of Thing (IoT) devices have taken over our lives. Everything from your refrigerator, thermostat, and light bulbs are talking to the cloud. This is generating an unprecedented amount of data that is traversing the Internet and needs to be stored somewhere, hopefully securely.
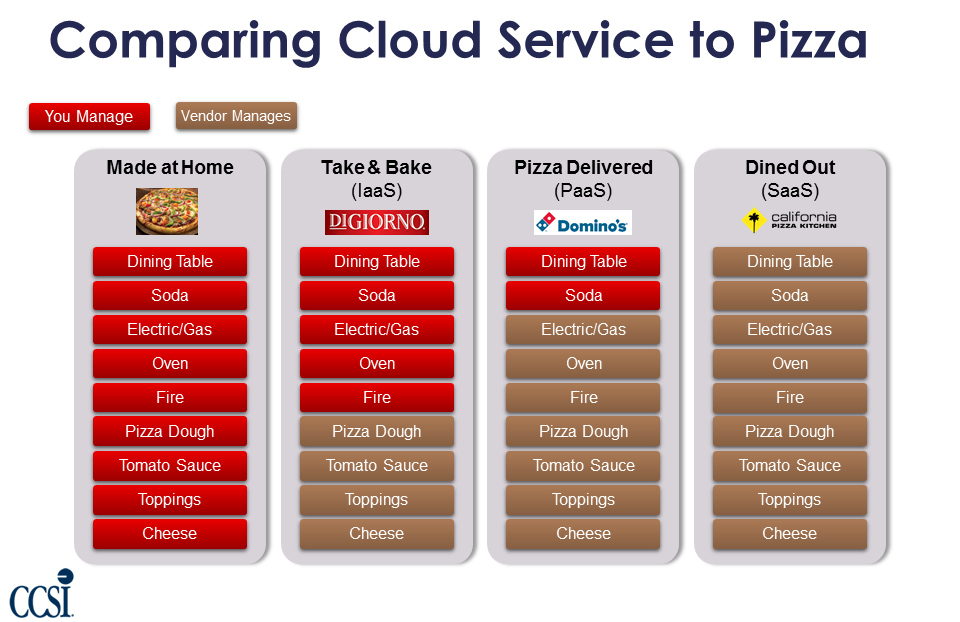
Many confuse the blurry line between the cloud and IoT. Below I will try to clear the air a little on this. IBM was kind enough to break down cloud computing into six categories:
1. Software as a Service (SaaS)
2. Platform as a Service (PaaS)
3. Infrastructure as a Service (IaaS)
4. Public Cloud
5. Private Cloud
6. Hybrid Cloud
IoT has a much smaller scope. It refers to devices other than computers and smartphones that connect to the Internet. Anything from your Tesla, to your Ring doorbell, LG fridge, and Nest thermostat can connect via the Internet of Things.
Google has created a nice description of the top three level components in an IoT environment.

A device includes hardware and software that directly interact with the world. Devices connect to a network to communicate with each other, or to centralized applications. Devices might be directly or indirectly connected to the internet.
A gateway enables devices that are not directly connected to the Internet to reach cloud services. Although the term gateway has a specific function in networking, it is also used to describe a class of device that processes data on behalf of a group or cluster of devices. The data from each device is sent to Cloud Platform, where it is processed and combined with data from other devices, and potentially with other business-transactional data.
As more and more IoT devices make their way into the world, deployed in uncontrolled, complex, and often hostile environments, securing IoT systems presents a number of unique challenges. According to Eclipse IoT Working Group’s 2017 IoT developer survey, security is the top concern for IoT developers. Going back to IBM again, they have put together a list of the top 10 IoT security challenges:
1. Secure constrained devices
2. Authorize and authenticate devices
3. Manage device updates
4. Secure communication
5. Ensure data privacy and integrity
6. Secure web, mobile, and cloud applications
7. Ensure high availability
8. Detect vulnerabilities and incidents
9. Manage vulnerabilities
10. Predict and preempt security issues
Incorporating security by default – where security features are configured at their most secure settings at all times, including before, during, and after development enables you to maintain data privacy and integrity, while delivering highly available IoT data, apps, and services.
CCSI has the expertise on staff and the service offering to provide any or all of the services above to assist you in your migration to the cloud. We are a certified Microsoft and AWS Cloud Partner. Contact us for more information or to receive a free cloud migration assessment.
Author Bio: Joe Goldberg is the Senior Cloud Program manager at CCSI. Over the past 15+ years, Joe has helped companies to design, build out, and optimize their network and data center infrastructure. As a result of his efforts, major gains in ROI have been realized through virtualization, WAN implementation, core network redesigns, and the adoption of cloud services. Joe is also ITIL certified.








