Cloud security is the protection of data, applications, and infrastructures involved in cloud computing. Just like on-prem IT security, cloud security still has concerns like unauthorized data leaks, weak access controls, susceptibility to attacks, and threats to availability.
Like any computing environment, cloud security requires administrators to do their standard housekeeping:
- Know that the data and systems are secure.
- Maintain visibility of current security posture.
- Rapid alerting and process and policy to respond.
- Can trace and respond to unexpected and unknown events.
Shared Security Model
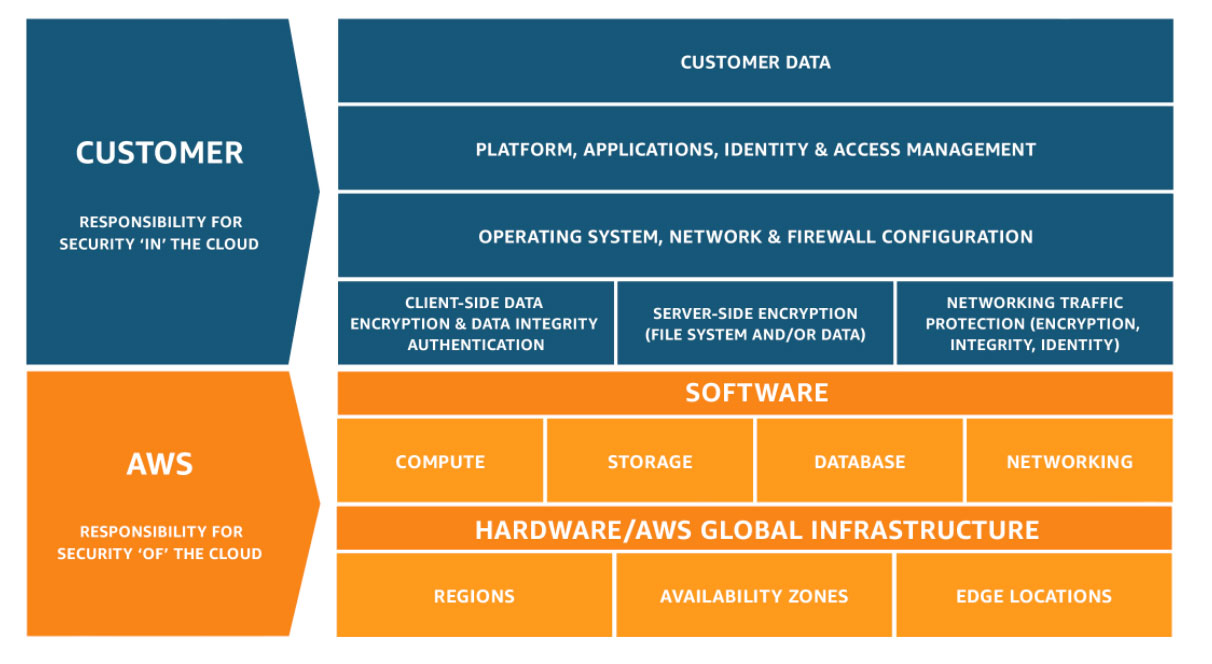
Part of the challenge in the cloud is the Shared Security Model. Many are mistakenly under the impression that they are either more secure in the cloud, because their provider is securing them or that they are completely insecure, because it is impossible to secure the cloud’s large attack surface. Both of these conclusions are incorrect. All the major cloud providers use the concept of a share responsibility model like below.
Below is the AWS Shared Security Model, but it is pretty much the same throughout all cloud providers.
CIS Controls
The Center for Internet Security (CIS) has put a lot of effort into creating controls and benchmarks to assist administrators of cloud environments. The CIS Controls are a general set of recommended practices for securing a wide range of systems and devices. CIS Benchmarks are guidelines for hardening specific operating systems, middleware, software applications, and network devices. The need for secure configurations is referenced throughout the CIS Controls.
Both the CIS Controls and the CIS Benchmarks are developed by communities of experts using a consensus-based approach and the information is freely available on their site.
Note though that the CIS Controls are not a replacement for any existing regulatory, compliance, or authorization scheme. The CIS Controls map to most major compliance frameworks such as the NIST Cybersecurity Framework, NIST 800-53, ISO 27000 series and regulations such as PCI DSS, HIPAA, NERC CIP, and FISMA. Mappings from the CIS Controls have been defined for these other frameworks to give a starting point for action.
We’ll start with a brief overview of the 20 CIS controls.
Basic CIS Controls
- Inventory and Control of Hardware Assets
- Inventory and Control of Software Assets
- Continuous Vulnerability Management
- Controlled Use of Administrative Privileges
- Secure Configuration for Hardware and Software on Mobile Devices, Laptops, Workstations and Servers
- Maintenance, Monitoring and Analysis of Audit Logs
Foundational CIS Controls
- Email and Web Browser Protections
- Malware Defenses
- Limitation and Control of Network Ports, Protocols and Services
- Data Recovery Capabilities
- Secure Configuration for Network Devices, such as Firewalls, Routers and Switches
- Boundary Defense
- Data Protection
- Controlled Access Based on the Need to Know
- Wireless Access Control
- Account Monitoring and Control
Organizational CIS Controls
- Implement a Security Awareness and Training Program
- Application Software Security
- Incident Response and Management
- Penetration Tests and Red Team Exercises
In future blogs, we will dive deeper into each of the Control groups.
Author Bio: Joe Goldberg is the Senior Cloud Program manager at CCSI. Over the past 15+ years, Joe has helped companies to design, build out, and optimize their network and data center infrastructure. As a result of his efforts, major gains in ROI have been realized through virtualization, WAN implementation, core network redesigns, and the adoption of cloud services. Joe is also ITIL certified.









hi,
Nice article, thanks a lot for sharing the same.
I enjoyed reading your article.