Outsourcing is popular more than ever now, especially taking into account the current conditions that contribute to everyone going remotely, its relatively low pricing and the high quality of external specialists’ work. As a result, many businesses seek remote developers. This practice entails many benefits and risks including the responsibility and security of your internal data. And that’s for a reason.
According to the research led by Verizon, 30% from the reported breaches that involved more than 40 000 incidents included internal actors meaning that the breach was either initiated from the inside or there were social engineering attacks aimed at people who had access to sensitive data.
So when you collaborate with people who may require access to your website, it’s required to dive deeper into this topic to find out all the peculiarities and default features of different Operation Systems, malicious attacks nature, and brute force protection as well as other security essentials. This info will help you protect yourself from unpleasant consequences such as data leakage, stealing personal information or destroying application assets. So let’s find some basic steps on how to securely share access with a developer:
Strive to provide minimum access creating separate users
The common way to share as minimum info as possible is initiating the project only via sharing Teamviewer access, however, depending on the project complexity, it’s not always applicable. It’s advisable to share FTP access to a separate directory or instead granting manage rights to a single database instead of sharing complete control panel access. This will minimize the risk of interference with other sensitive resources that are not related to the website in question (i.e. there will be no way for a developer to get to your email or modify DNS records)
Whenever it’s possible, it’s advisable to create separate users for development purposes. Be it the users with the same privileges as already existing ones, having separate users for it will be beneficial in case you notice any suspicious activity and need to block these users right away.
If you manage the server where you have root access, never share this password since it’s the highest level of access and if something goes wrong, it’s easy to lose everything you have. It’s better to provide users with Sudo rights if such necessity occurs to make global server changes such as OS update or software install (i.e., any firewall set up, the majority of chatbots, or monitoring for your server). If you are on Linux server (by the way Linux offers the best-inbuilt security features compared to other OSs), you can use the following commands to create a Sudo user:
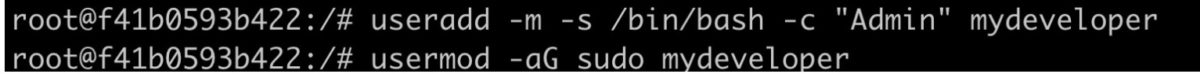
The first command includes the action of adding a user ‘useradd’, -m argument -s is responsible for shell directory which is, /bin/bash in our case is an operating directory, -c allows you to specify the comment which is ‘Admin’ in our case, and ‘mydeveloper’ part is responsible for the actual username that will be used for the login.
In the second command, we give superuser rights to your new user via ‘usermod’ -ag sudo allowing it to perform the actions that will be applicable globally.
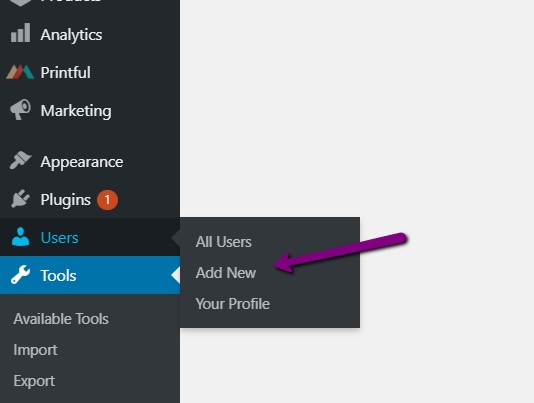
Some simple applications of this rule would include creating a separate admin user for some CMSs. Here are the instructions for WordPress (since it’s the most commonly used CMS on the market). If you run a simple eCommerce on Shared Hosting, logging of changes made of separate users may be done via the security plugins such as Wordfence or Sucuri that keep track on the login history for all the users, including contributors and send you automatic emails whenever any changes are made on your website such as post deletion.
You can create a separate Admin user by going to your WordPress dashboard > Users> Add new
On the second screen, you need to assign a corresponding role:
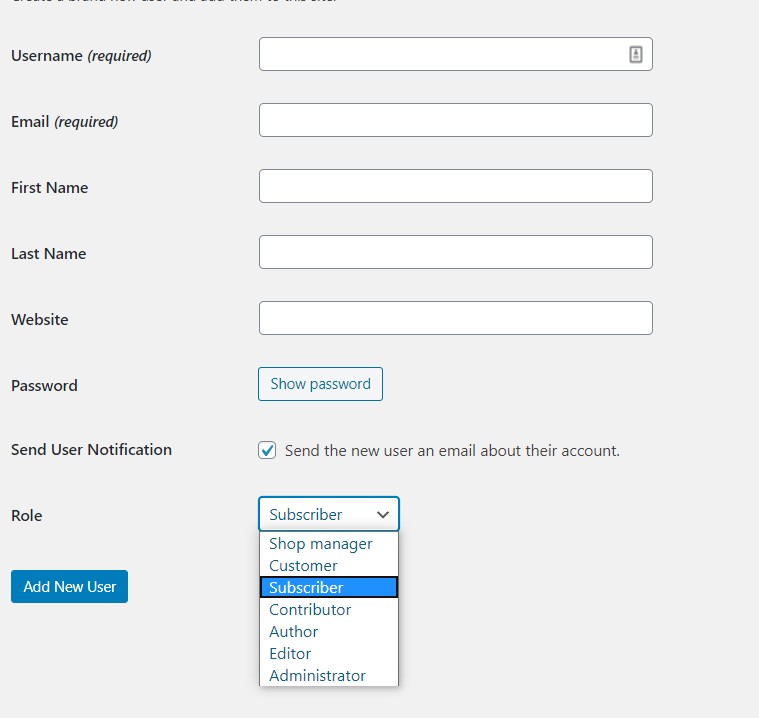
Most likely you will need to assign the ‘Administrator’ role to your developer, as this option is the only one among the present ones for a single WordPress website that allows plugins and themes management.
Avoid sharing these details
It goes without saying that sensitive details such as connecting your credit card details to make some software purchase or make any wire transfer from your banking account should be performed only on your end without sharing CVV code and security passphrases. If it’s not an option, it’s better to agree on a cost-reimbursable contract with a person engaged in outsourcing. In addition, it’s better to avoid disabling 2FA authentication to third-party accounts involved in the project and during the development and discuss the access hours so that you can be available to jump in the call with a developer to provide this code and just in case keep a track on what is going on.
Develop a security policy within your company
Even if you are a solopreneur or a small startup consisting of 3 people, it never hurts to keep a strict security policy when hiring third-party organizations. The security rules should include regular password changes for all your employees and working resources including server access, admin dashboard access (if applicable), and corporate emails. If you have no previous experience with making security policies you may start with searching for information available online with tips like security checklists for a website to make sure that nothing is missed. Again, we are using the WordPress example here, but you may adjust it depending on the CMS or a custom solution that is relevant to your organization. In addition to the regular password, take care of ad-hoc changes when any of your employees leave the company, or your cooperation with outsourced personnel is finished. Pay special attention to the level of access you plan to provide to outsourced personnel and warn your on-site people about it to avoid any possible data leakages. In addition, it’s recommended to conduct regular security training for your new employees.
Wrap Up
Following these tips will minimize security breaches initiated from the inside but it’s only one step towards the security of your website and the sensitive information within your company. Other steps include more expensive methods such as specialized software, closing vulnerable ports for incoming requests and investing in trusted Firewall and Anti-malware solutions, making internal resources accessible only from corporate VPN.
It’s not recommended to choose cut-corner strategies such as using non-licensed software or neglect security code reviews done by professionals as well as pen tests since it will cost you much more to cover the reputation and monetary losses in case of an unexpected situation.

Author Bio: Stewart Dunlop looks after content marketing at Udemy and has a passion for writing articles that users will want to read. In his free time, he likes to play football and read Stephen King.
Stewart is a guest blogger. All opinions are his own.







